

There can be more than one configuration - so called profiles. But only one of these profiles can be active. The active profile can be chosen with the combo box at the status bar. If you want to create, modify or delete a profile, you have to activate the configuration page and chose there in the combo box the profile. Any changes to a profile get active only after pressing the save button.
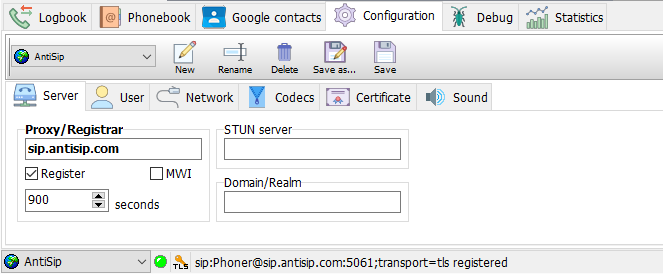
Enter here the address of your SIP server. There are two kinds of SIP servers:
Most VoIP providers are using the same address for registrar and proxy. Therefore only one address is configurable in PhonerLite. The address might be a name (e.g. "sipgate.de") or an IP address (e.g. "217.10.79.9"). The default port for SIP signaling is 5060. If the proxy/registrar uses a different port, you can concatenate it by a leading colon (e.g. "sipgate.de:5060").
Using the checkbox "Register" you can select whether to register or not.
Normally a PC got a private IP address. If the destination is out of this private network, your public IP address have to be within the SIP messages transmitted to the server. For retrieving this public IP address STUN is used and therefore a STUN server must be configured.
Even using STUN there is no guarantee for a functional communication. In case of communication errors such restrictive firewalls must be configured for passing messages using UDP ports 5060 and 5062 to the PC running PhonerLite.
SIP uses a different address format than in public switched telephone networks.To enable the input of normal phone numbers, PhonerLite needs some information for extend this number to the right SIP format . Default is using the proxy/registrar address. If this address differs from the needed domain you have to enter this domain here.
Example: The address of the proxy/registrar is "sip.domain.com". But called addresses must use the domain "domain.com" - see, there is a missing sub domain "sip". A valid destination address would be "49891234567@domain.com". For this case you have to enter "domain.com" in to this field.
There is no must be for this domain, because users can dial complete SIP addresses manually too.
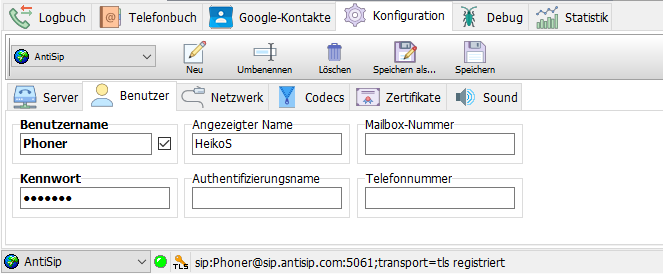
The username is used for authentication . With this username you have to be registered at the SIP proxy/registrar. You get this name from your VoIP provider. Within message exchange this name is transmitted unencrypted.
Using this password /a> the username can be validated by the SIP server. The password is encrypted by MD5 within the messages.
All saved profiles (sipper.ini) contain all settings including encrypted passwords.Don't give this file to other people, because they can use your accounts without modifications!
If authentication is required (see Password) a authentication name may be used that is different from username. In most cases the same value is used and therefore this field can be left empty.
You can enter here any text you want, but normally your real name should be here.
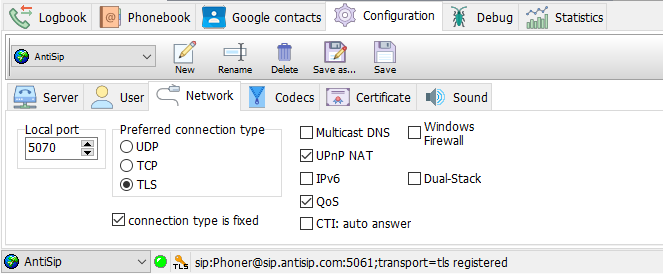
The local signaling port you can choose here. For speech transmission (RTP) the port with a value of additional 2 will be used. So if the signaling port is 5060 the RTP port will be 5062. Any further call use the port increased by 2 again.
If a configured port is used by a another application, a port given by the system is used then.
Incoming connections are always possible using UDP, TCP and TLS. For outgoing connections (registration and call initiation) will use the preferred connection type.
If this option is enabled, several PhonerLite instances in the same LAN will find each other automatically. A new index page with the name "Neighbours" will be shown. Using drag&drop with that entries to the call list will initiate a direct connection to that instance.
Via UPnP PhonerLite can retrieve the public IP address of the router and can set a port forwarding automatically. The router has to support UPnP and the control via UPnP.
If UPnP control is supported by the router, this procedure is preferred against STUN.
With Windows Vista and newer versions IPv6 is usable as an alternative to IPv4 . The complete infrastructure has to support IPv6 too. IPv4 and IPv6 is not usable at the same time in PhonerLite!
A codec is the short word for "coder and decoder"..
In this window you can disable individual codecs and change their priority. The most preferred codec should be on top of the list. If this preferred codec is used belongs of the counterpart - if it supports this codec too.
The shown data rates are net values. In practice these values are much higher because of the encapsulation of speech data in RTP , UDP and finally in IP packets.The gross data rate for a G.711 codec is about 80 kBits/s. This is too much for modem and ISDN dial-up connections! But if such connection is used, these codecs should be disabled here.
Following codecs are supported by PhonerLite:
Echo Cancellation means analyzing of data to be sent and the filtering of containing received data. By activating this option you can avoid that you your microphone records data from the speakers.
"silence detection" means the analysis of recorded data from the microphone (what should be sent). If this data doesn't contain any audible voice activities, this can be detected.
There are three options for this:
Everybody has to find out the optimal setting by himself.
If speech data should be encrypted, you can activate the option SRTP . To avoid key exchange in clear text, SRTP should only be used in conjunction with TLS..
The peer (phone or provider) must support SRTP too. The actual implementation is tested against Grandstream GXP2000 and the German VoIP provider dus.net .
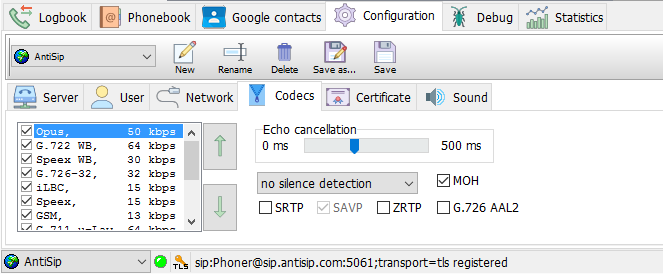
To enable end-to-end encryption of audio data for pure IP-to-IP calls, key exchange can be used without TLS.
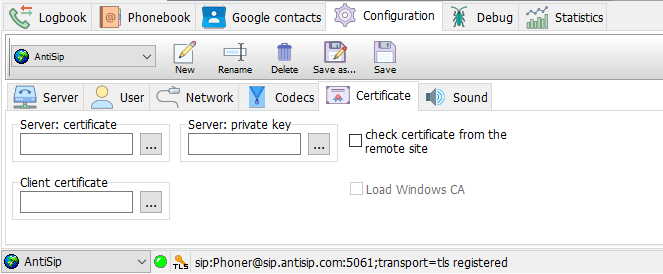
Certificates are needed by secured connections using TLS . For connections to a server, this server may request a client certificate. Such client certificate authorizes the user of PhonerLite to the server. You can load such certificate by pressing the "..." button or by typing the filename directly. If no client certificate is configured a built in certificate is used.
If you want to enable peer-to-peer connections, you need to configure a server certificate.
The configured certificate files must include a key and the certificate itself. The files should like like:
-----BEGIN RSA PRIVATE KEY-----
[...]
-----END RSA PRIVATE KEY-----
-----BEGIN CERTIFICATE-----
[...]
-----END CERTIFICATE-----
The location of the configuration files depend on the write access permissions. If the program folder has full write access permissions, this folder is used for configigurations files too, else this folder is used: %APPDATA%\PhonerLite. Following files will be created and handled by the application: